Types of cybersecurity In today’s hyper-connected digital world, cybersecurity is no longer limited to protecting computers alone. Organizations now operate across cloud platforms, mobile devices, smart systems, and global networks — each creating new opportunities for cybercriminals.
Cybersecurity refers to the collection of technologies, processes, and practices designed to protect systems, networks, applications, and data from unauthorized access, attacks, or damage. Modern cyber threats range from phishing scams and ransomware to advanced state-sponsored intrusions that remain hidden for months.
To build strong protection, cybersecurity is divided into specialized domains. Each domain focuses on defending a specific digital environment and addressing particular threats.
This guide explores 8 major types of cybersecurity and the real threats involved in each.
Why Cybersecurity Matters Today
Businesses, governments, and individuals rely heavily on digital systems. Sensitive information such as financial data, personal identities, and intellectual property exists online — making it a prime target.
Cyberattacks can lead to:
- Financial loss
- Data breaches
- Identity theft
- Operational downtime
- Reputational damage
Modern attacks are also becoming smarter. AI-generated phishing emails and impersonation scams now appear highly realistic, making detection harder than ever.
Because threats vary across environments, types of cybersecurity is divided into multiple protection layers.
1. Network Security
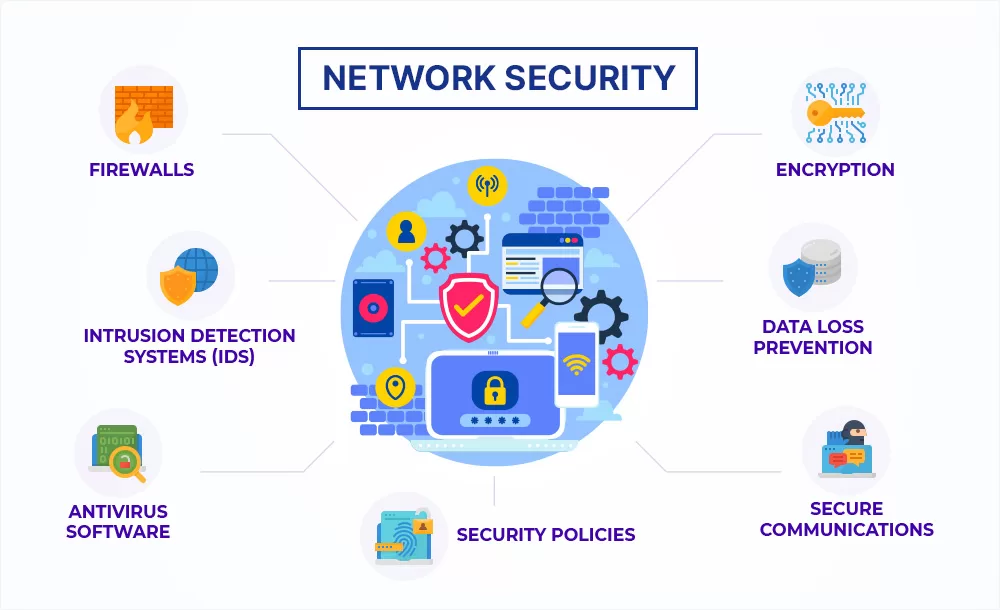
What It Is
Network security focuses on protecting internal and external networks from unauthorized access, misuse, or disruption. It ensures secure communication between devices and prevents attackers from entering organizational systems.
Common security mechanisms include:
- Firewalls
- Intrusion detection systems
- VPNs
- Traffic monitoring
- Encryption protocols
Threats Involved
- Distributed Denial of Service (DDoS) attacks that overload servers
- Network sniffing and interception
- Unauthorized remote access
- Malware spreading across networks
Attackers often exploit weak configurations or outdated infrastructure to infiltrate systems.
2. Application Security

What It Is
Application security protects software and web applications throughout their lifecycle — from development to deployment.
Secure coding practices and vulnerability testing help prevent attackers from exploiting software weaknesses.
Threats Involved
- SQL injection attacks
- Cross-site scripting (XSS)
- Code injection
- Zero-day vulnerabilities
A single vulnerable application can expose an entire database to attackers.
3. Information and Data Security

What It Is
Information security safeguards sensitive data from unauthorized access or alteration. It follows the well-known CIA triad:
- Confidentiality
- Integrity
- Availability
This domain protects customer data, business records, and intellectual property.
Threats Involved
- Data breaches
- Insider threats
- Identity theft
- Unauthorized data modification
Since data is one of the most valuable digital assets, attackers often target databases directly.
4. Endpoint Security

What It Is
Endpoint security protects individual devices connected to a network, including:
- Laptops
- Smartphones
- Servers
- Workstations
- Tablets
Each device acts as a potential entry point for attackers.
Threats Involved
- Ransomware infections
- Malware downloads
- Phishing attachments
- Device theft or compromise
Modern security models often follow a Zero Trust approach, verifying every device before granting access.
5. Cloud Security

What It Is
Cloud security focuses on protecting data, applications, and infrastructure hosted on cloud platforms.
As organizations migrate to cloud environments, shared responsibility models require both providers and users to maintain security controls.
Threats Involved
- Misconfigured storage buckets
- Account hijacking
- Data leakage
- Unauthorized API access
Cloud attacks frequently occur due to poor access management rather than platform vulnerabilities.
6. Website and Web Security

What It Is
Website security ensures that websites, servers, and web applications remain protected from online exploitation.
It covers databases, source code, hosting environments, and user interactions.
Threats Involved
- Website defacement
- Credential theft
- Fake login pages
- Lookalike domain attacks used for impersonation fraud
Compromised websites can distribute malware to thousands of visitors instantly.
7. Internet of Things (IoT) Security
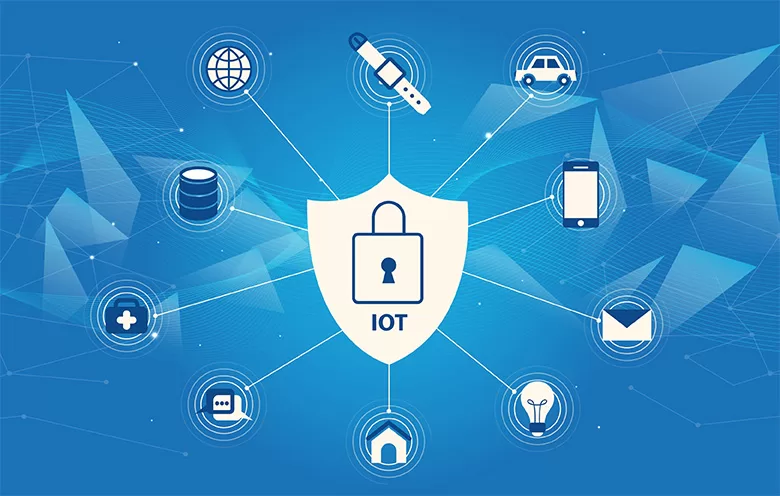
What It Is
IoT security protects connected smart devices such as:
- Smart home appliances
- Cameras
- Wearables
- Industrial sensors
With billions of connected devices, IoT expands the attack surface significantly.
Threats Involved
- Man-in-the-Middle (MITM) attacks
- Device hijacking
- Botnet creation
- Data interception
Even one vulnerable device can compromise an entire network.
8. Disaster Recovery and Cyber Resilience

What It Is
Disaster recovery focuses on restoring systems and operations after cyber incidents or technical failures.
Rather than preventing attacks, this domain ensures rapid recovery and business continuity.
Key Components
- Backup strategies
- Incident response plans
- Risk assessments
- System restoration procedures
Threats Addressed
- Ransomware shutdowns
- Infrastructure attacks
- Data loss incidents
- Large-scale cyber intrusions
Advanced Persistent Threats (APTs) — long-term stealth attacks — often require strong recovery planning due to their deep system penetration.
Common Cyber Threats Across All Domains
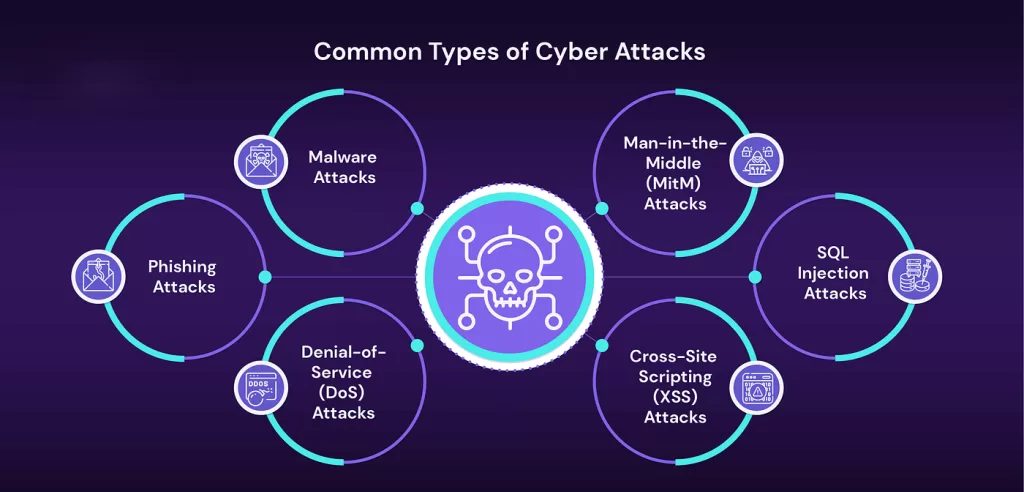
Regardless of the cybersecurity type, several threats appear repeatedly:
Malware
Malicious software designed to damage or steal data.
Phishing
Social engineering attacks tricking users into revealing credentials.
Ransomware
Encrypts systems and demands payment for recovery.
Insider Threats
Employees or partners misusing legitimate access.
AI-Driven Attacks
Cybercriminals increasingly use AI to automate scams and impersonation techniques.
How Organizations Build Strong Cybersecurity
Effective cybersecurity combines multiple strategies:
- Multi-layered defense systems
- Continuous monitoring
- Employee awareness training
- Regular updates and patching
- Identity and access management
No single security tool can stop every attack — protection must exist across all domains simultaneously.
Future of Cybersecurity
Cybersecurity is evolving rapidly due to:
- Artificial intelligence
- Cloud adoption
- Remote work environments
- Smart device expansion
Experts predict that cyber defense will increasingly rely on automation, behavioral analytics, and AI-powered threat detection systems.
Organizations that invest in proactive security today are far better prepared for tomorrow’s digital risks.
Conclusion
Types of Cybersecurity is not a single solution but a layered ecosystem of protections. From network security and cloud protection to IoT defense and disaster recovery, each domain plays a critical role in safeguarding digital environments.
Understanding these 8 types of cybersecurity and their associated threats helps individuals and organizations design stronger defenses against modern cybercrime.
As technology advances, cybersecurity awareness and preparedness will remain essential skills in the digital age.
Want to learn about Cyber Security?, Kaashiv Infotech Offers, Cyber Security Course, or Networking Course & More, Visit www.kaashivinfotech.com.