Malware
Malware is malicious software that is planned to damage and destroy computers and computer systems. Examples of common includes viruses, worms, Trojan viruses, spyware, adware, and ransomware. It typically performs its malicious activities after it is fixed into the computer system.
Table Of Content
Types of Malware
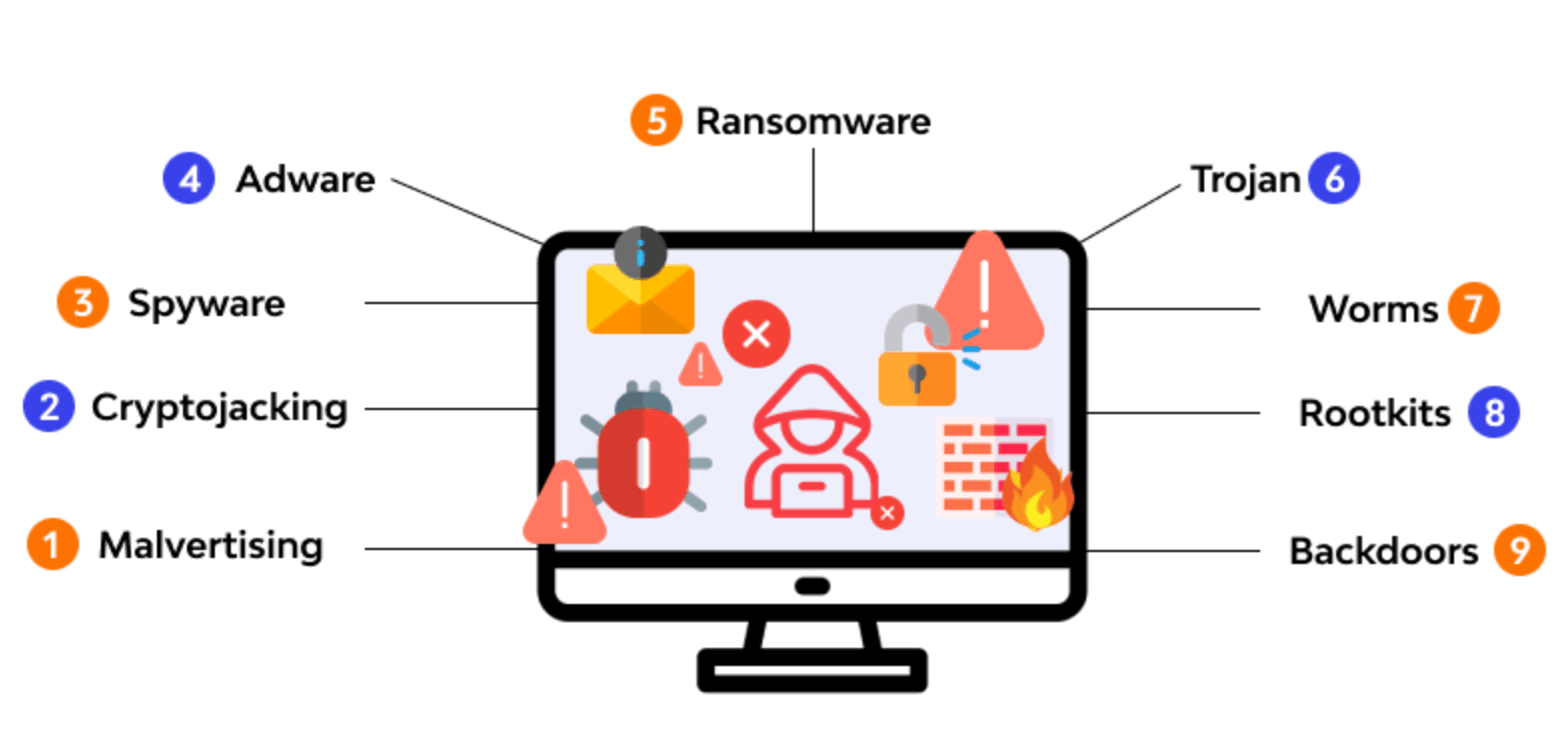
Trojans
- A Trojan disguised itself as legitimate software with the purpose of tricking you into executing malicious software on your computer
Spyware
- It attacks your computer and attempts to steal your personal information such as credit card or banking information, web browsing data and passwords to various accounts.
Adware
- It is unwanted software that displays advertisements on your screen. Adware collects personal information from you to serve you with more personalized ads.
Rootkits
- Programs that provide privileged (root-level) access to a computer. Rootkits differ and hide themselves in the operating system.
Ransomware
- It is designed to encrypt your files and block access to them until a ransom is paid.
Worms
- A worm replicates itself by infecting other computers that are on the same network. They are planned to consume bandwidth and interrupt networks.
Keyloggers
- It keep track of your keystrokes on your board and record them on a log. This information is used to gain unauthorized access to your accounts.
Categories of Malware Attacks
- Email attachments containing malicious code can be opened, and then implemented by unsuspecting users. If those emails are forwarded, the malware can spread even deeper into an association, further compromising a network.
- File servers, such as those based on common Internet file system (SMB/CIFS) and network file system (NFS), can enable to spread quickly as users access and download infected files.
- File-sharing software can allow to duplicate itself onto detachable media and then on to computer systems and networks.
- Peer to peer (P2P) file sharing can introduce by sharing files as apparently harmless as music or pictures.
- Remotely usable vulnerabilities can enable a hacker to access systems regardless of geographic location with little or no need for participation by a computer user.
How to Prevent Malware from Installation ?
Installing Legit Software Only: Always install legit software. Software from an in-legit manner often contains malware in them.
Installing Software from the Unknown Source: Always install software from known sources. Do not download software from any website apart from getting install from a known source.
Updating Operating System Updates: Install OS updates as these updates often contain an efficient definition for the detection of malware.
Updating Software Patches: Installed software also gets patches. Therefore, one needs to install such patches to prevent it.
Installing Anti-Virus: Install anti-virus and anti-malware software to stop any such malicious activities.
Malware Detection
The following is how you can detect malware-infected systems or networks. These are the signs that you need to look for:
- Really slow and unresponsive system
- Undeletable files
- Random folders or shortcuts inside folders
- Problems while shutting down due to certain running files or programs
- Change in default settings of PC
- Unnecessary running services or programs using up the processing power of the CPU
- Reboot issues
- Auto shutdown
- Unnecessary traffic patterns or traffic to destinations you never targeted
- Similar malware warnings by the antivirus on the network
Malware Removal
Below steps need to be taken after the detection of malware in the computer or network:
- Removal: Sanitisation of the infected PC or network
- Prevention: Confirm that the system and network is safe from similar events
For the removal process, the following basic steps can be taken:
- Remove the system from the network, and remove all internet and intranet connectivity
- Do not connect external drives as that might spread the malware to other systems
- Perform a full scan on the PC with an efficient antivirus program
- Reboot the PC and update all software patches
If the removal is not successful, format the system and take the following prevention steps:
- Schedule systematic full scans using a legitimate antivirus
- Keep your OS up to date
- Avoid opening emails or attachments from untrusted sources
- Scan external drives before inserting them into the system
- Avoid downloading software from illegal sources
- Backup critical information on an external drive
- Avoid macro in Excel, if not required
Protection
To protect your organization against malware, you need a full, enterprise-wide protection strategy. Commodity threats are exploits that are less sophisticated and more simply detected and prevented using a mixture of antivirus, anti-spyware, and vulnerability protection features along with URL filtering and Application identification skills on the firewall.