Security Threat to E-Commerce
Threat to E-Commerce
E-commerce threat is occurring by using the internet for unfair means with the intention of stealing, fraud and security breach. There are various types of e-commerce threats. The most common security threats are an electronic payments system, e-cash, data misuse, credit/debit card frauds, etc.
Electronic payments system:
- With the rapid development of the computer, mobile, and network technology, e-commerce has become a routine part of human life. E-commerce processing is user-friendly and less time consuming than manual processing.
Some of them are:
The Risk of Fraud
- An electronic payment system has a huge risk of fraud.
- The computing devices use an identity of the person for authorizing a payment such as passwords and security questions.
- These authentications are not full proof in determining the identity of a person.
Risk of Tax Evasion
- Internal Revenue Service law requires that every business declare their financial transactions and provide paper records so that tax compliance can be verified. The problem with electronic systems is that they don't provide cleanly into this paradigm.
Risk of Payment Conflicts
- Electronic payment systems, the payments are handled by an automated electronic system, not by humans. The system is prone to errors when it handles large amounts. of payments on a frequent basis with more than one recipients involved.
E-cash
- E-cash is a paperless cash system which facilitates the transfer of funds anonymously. E-cash is free to the user while the sellers have paid a fee for this. The most common examples of e-cash system are transit card, PayPal, GooglePay, Paytm, etc.
- E-cash has four major components-
- Issuers - Banks or a non-bank institution.
- Customers - Users who spend the e-cash.
- Merchants or Traders - Vendors who receive e-cash.
- Regulators - Related to authorities or state tax agencies.
Some of the major threats related to e-cash system are-
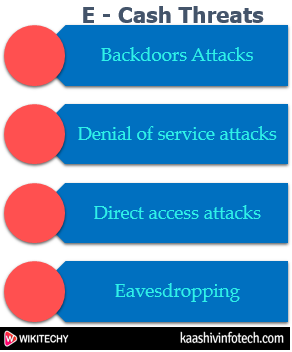
E-Cash Threat
Read Also
Backdoors Attacks
- It is a type of attacks which gives an attacker to unauthorized access to a system by bypasses the normal authentication mechanisms. It works in the background.
Denial of service attacks
- A denial-of-service attack ( DoS attack ) is a security attack in which the attacker takes action that prevents the legitimate (correct) users from accessing the electronic devices.
Direct Access Attacks
- Direct access attack is an attack in which an intruder gains physical access to the computer to perform an unauthorized activity and installing various types of software to compromise security.
Eavesdropping
- This is an unauthorized way of listening to private communication over the network.
Credit/Debit card fraud
- A credit card allows us to borrow money from a recipient bank to make purchases.
- A debit card is of a plastic card which issued by the financial organization to account holder who has a savings deposit account that can be used instead of cash to make purchases. The debit card can be used only when the fund is available in the account.
Some of the important threats associated with the debit/credit card are-
ATM (Automated Teller Machine)
- It is the favorite place of the fraudster from there they can steal our card details. Some of the important techniques which the criminals opt for getting hold of our card information is:
Skimming
- It is the process of attaching a data-skimming device in the card reader of the ATM. By doing this, the criminals get to know the details of the Card number, name, CVV number, expiry date of the card and other details.
Unwanted Presence
- It is a rule that not more than one user should use the ATM at a time.
Vishing/Phishing
- Phishing is an activity in which an intruder obtained the sensitive information of a user such as password, usernames, and credit card details, often for malicious reasons, etc.
- Vishing is an activity in which an intruder obtained the sensitive information of a user via sending SMS on mobiles.
Online Transaction
- Online transaction can be made by the customer to do shopping and pay their bills over the internet. Some important ways to steal our confidential information during an online transaction are-
- Downloading software which scans our keystroke and steals our password and card details.
- Redirecting a customer to a fake website which looks like original and steals our sensitive information.
- Using public Wi-Fi
POS Theft
- It is commonly done at merchant stores at the time of POS transaction.
