Types of Cyber Attackers
Types of Cyber Attackers
Attackers use every tools and techniques they would try and attack to get unauthorized access.
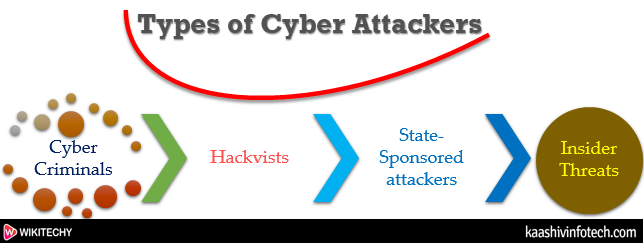
Types Of Cyber Attackers
Cyber Criminals
- Cyber criminals are individual or group of people who use technology to commit cybercrime with the intention of stealing sensitive company information or personal data and generating profits.
- Cybercriminals use computers in three broad ways to do cybercrimes
- Select computer as their target - Attack other people's computers to do cybercrime, such as spreading viruses, data theft, identity theft, etc.
- Uses the computer as their weapon - Use the computer to do conventional crime such as spam, fraud, illegal gambling, etc.
- Uses the computer as their accessory - They use the computer to steal data illegally.
Hacktivists
- Hacktivists are individuals or groups of hackers who carry out malicious activity to promote a political agenda, religious belief, or social ideology.
- According to Dan Lohrmann, chief security officer for Security Mentor, a national security training firm that works with states said "Hacktivism" is a digital disobedience.
State-sponsored Attacker
- State-sponsored attackers have particular objectives aligned with either the political, commercial or military interests of their country of origin. These type of attackers are not in a hurry.
Read Also
Insider Threats
The insider threat is a threat to an organization's security or data that comes from within.
Insider threats are-
Malicious
- Malicious threats are attempts by an insider to access and potentially harm an organization's data, systems or IT infrastructure.
- Insiders may also become threats when they are disguised by malicious outsiders, either through financial incentives or extortion.
Accidental
- Accidental threats are threats which are accidently done by insider employees.
Negligent
- This threats in which employees try to avoid the policies of an organization put in place to protect endpoints and valuable data. There is nothing wrong with these acts, but they can open up to dangerous threats nonetheless.
