System Hacking
System hacking
It is defined as the compromise of computer systems and software to access the target computer and steal or misuse their sensitive information. Here the malicious hacker exploits the weaknesses in a computer system or network to gain illegal access to its data or take illegal advantage.
Table Of Content
Phases of System Hacking
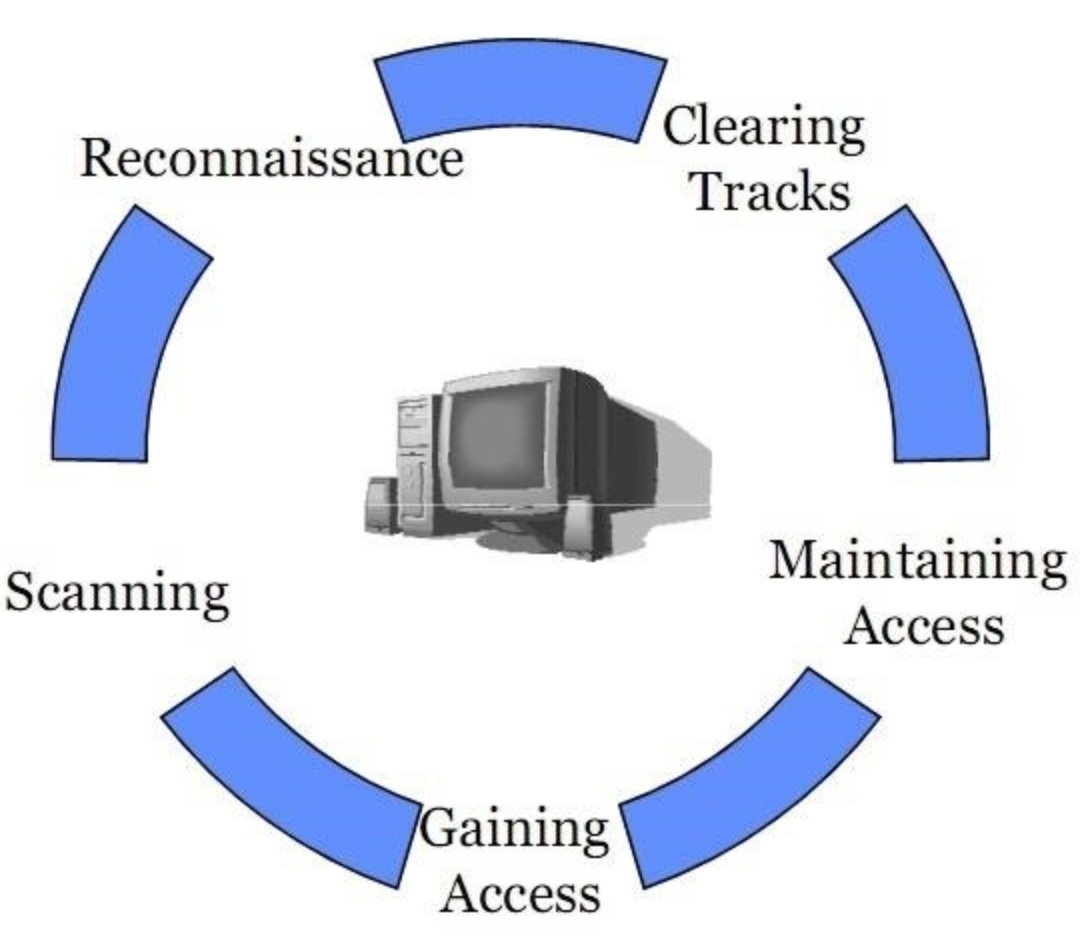
- Reconnaissance – Majorly used to gather data
- Scanning – Used to gather more intelligence on the data
- Gaining access – Takes control of one or more network devices to extract data.
- Maintaining access – Gains more data from the targeted environment
- Clearing tracks – Eliminate traces of detecting the attack.
How Hackers Perform System Hacking ?
A hacker can hack the computer system because the hacker knows the actual work of computer systems and software inside the system. For this, a hacker has information about the systems, networking, and knowledge of other areas related to computer science. Anyone who is using a computer and is connected to the internet is vulnerable to malicious hackers threats. These online villains generally use viruses, malware, Trojans, worms, phishing techniques, email spamming, social engineering, exploit operating system vulnerabilities, or port vulnerabilities to access any victim’s system.
What can these predators do using after compromising the system
When your PC gets connected to the internet, the hacker may execute the malware on your PC and transmits the personal, financial, and essential information without your knowing consent. These hackers can blackmail the victim for the money by stealing that sensitive information from your computer, which you don’t want to expose. After compromising the victim’s system, the hacker can do these following things:
- Steal money and credit card details while the victim is doing e-marketing or online transaction.
- Sell victim’s information to third parties who may use this information for illegal purposes.
- Create traffic to shut down your website.
- Ruin the victim’s data by deleting the files.
- Steal files and folders.
- Hijack victim’s username and password.
- Get access to the servers and manipulate the files, programs, etc.
Linux System Hacking
Linux is an Operating System (OS) collected user the model of open-source software development and distribution and is based on Unix OS created by Linus Torvalds.
Now to hack a Linux-based computer system and get access to a password protected Linux system, we have to know Linux’s basic file structure. As we know, Linux is considered to be the most secure OS to be hacked or cracked, but in the world of Hacking, nothing is 100% secured.
Hackers usually use the following techniques to hack the Windows system.
- Linux hack using the SHADOW file.
- Hacker detects the bug on Linux distribution and tries to take advantage of it.
- Hackers is to bypass the user password option in Linux.
Windows Hacking
The user password of Windows OS, which looks after the Windows starts logging in, lets users protect the computer from getting illegal access. Selecting a strong password of more than eight digits is an excellent practice. Hereafter you can protect your files and folders from the hands of malicious users. There are several tricks and methods to crack a windows password. But, from the hacker’s point of view, if you can use social engineer your victim and find a Windows computer open, you can simply modify the existing password and give a new password that will be unaware of the victim or the owner of the computer.
Human Precautions against System Hacking
Carefully deal with friends’ requests from online social networking sites and emails.
Don’t open or click unnecessary emails from strangers or unknown senders.
Use exciting caution while entering chatrooms or dealing with chatrooms’ users online.
Continually check for the accuracy of the personal account.
How to protect your System from Hacking
- Internet Security Antivirus and Anti-malware software protection with definition updates.
- Use both way firewall and keep updating.
- Download the mandatory software from trusted sites only.
- Training using safe email protocols such as SSL, SMTPS, etc.
- Check whether the sites are HTTPS or not for better protected online services and transactions.
- Update the OS for better areas.
- Avoid doubtful websites.
- Increase the browser security settings.
- Directly delete those messages which you suspect to be spam.
- Try to use open software(s) and not the plagiarized ones because the plagiarized ones could be reverse-engineered. Hackers can attach monitoring or malicious tools and programs with the software.