SQL Injection Hacking
What Is SQL Injection ?
SQL Injection is a code-based vulnerability that permits an attacker to read and access complex data from the database. Attackers can bypass security measures of applications and use SQL queries to modify, add, update, or delete records in a database. A SQL injection attack can affect websites or web applications using relational databases such as MySQL, Oracle , or SQL Server. In current years, there have been many security cracks that resulted from SQL injection attacks.
Table Of Content
Types of SQL Injection
In-band SQLi – The attackers use the same communication channel to launch their attacks and collect outcomes.
Common types of in-band SQL injections are Error-based SQL injection and Union-based SQL injection.
- Error-based SQL injection – Here, the attacker executes actions that cause the database to create error messages. Using the error message, you can find what database it uses, the version of the server where the trainers are located, etc.
- Union-based SQL injection – UNION SQL operator is used in combining the results of two or more select statements generated by the database, to get a single HTTP response. You can craft your queries within the URL or combine multiple statements within the input fields and try to create a response.
Blind SQLi – Here, it does not transfer the data through the web application. The attacker cannot see the result of an attack in-band.
- Boolean-based SQL Injection – Attacker will send an SQL query to the database asking the application to return a different result depending on whether the query returns True or False.
- Time-based SQL Injection – The attacker sends an SQL query to the database, which makes the database wait for a specific amount of time before sharing the result. The response time helps the attacker to decide whether a query is True or False.
Out-of-bound SQL Injection – It is not popular, as it depends on the features that are enabled on the database server being used by the web applications. It can be like a misconfiguration error by the database administrator.
How Does SQL Work On a Website ?
A website has three main components – Frontend, Backend, and Database.
Frontend – A website is designed using HTML , CSS , and JavaScript
Backend – Here you have scripting languages such as Python , PHP , Perl, etc.
Database – The server side has databases such as MySQL, Oracle, and MS SQL Server, to execute the queries.
When you write a query, you usually send a get request to the website. Then, you receive a response from the website with HTML code.
Using the Postman API tool, you can test the responses that you get from various websites.
Demo on SQL Injection
- Go to Google Chrome or any web browser and search for owasp broken web apps
- Click on the sourceforge.net link
- Select the Download option to download the OWASP Broken Web Applications Project
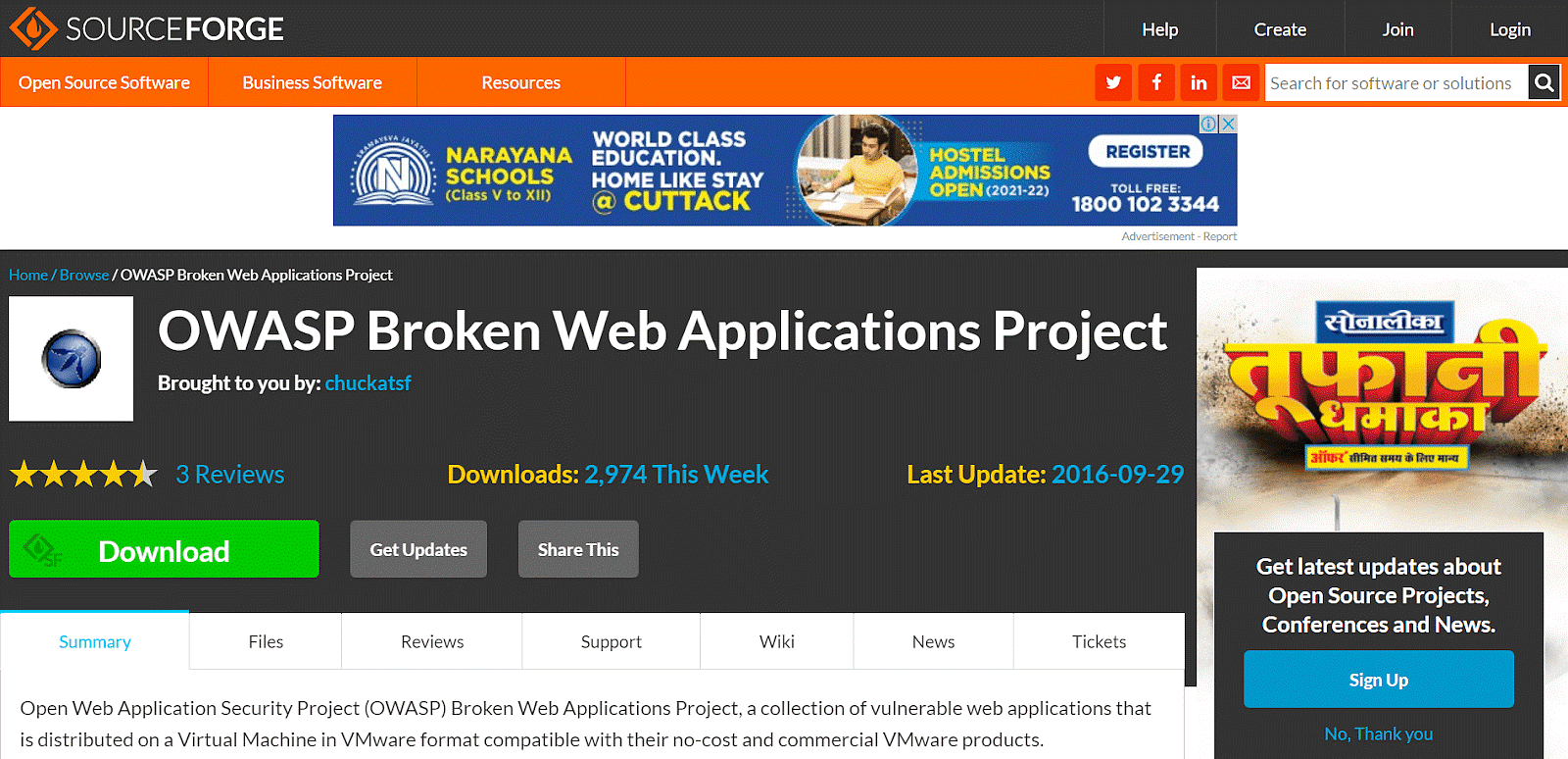
This application has been established by the Open Web Application Security Project that periodically releases the top 10 risks that an application will face for a specific year. It has a collection of weak web apps that are distributed on a Virtual Machine.
Note: Performing SQL Injection in the real-world on any website is illegal.
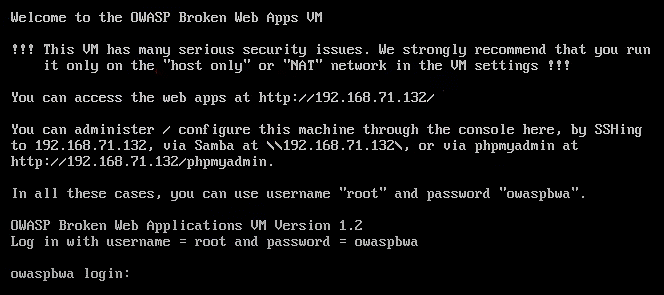
- After downloading the OWASP Broken Web Apps virtual machine, open it on a VMware workstation.
- You can see the IP address of the machine. In this case, it’s 192.168.71.132
- Use the IP address mentioned above and open it on a browser
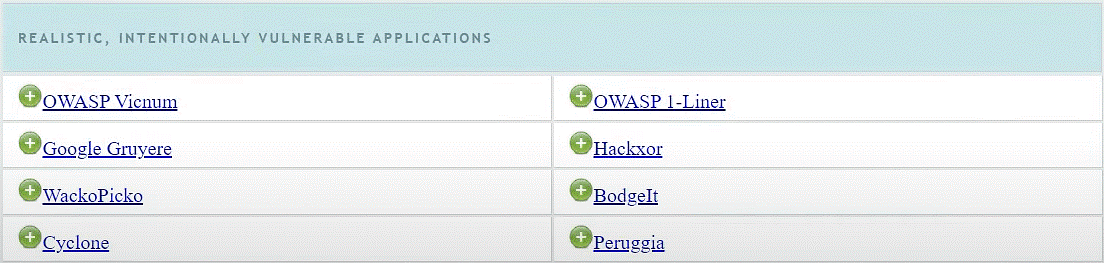
You will find training applications, and realistic, intentionally vulnerable applications.
You can also find old versions of real applications and much more.
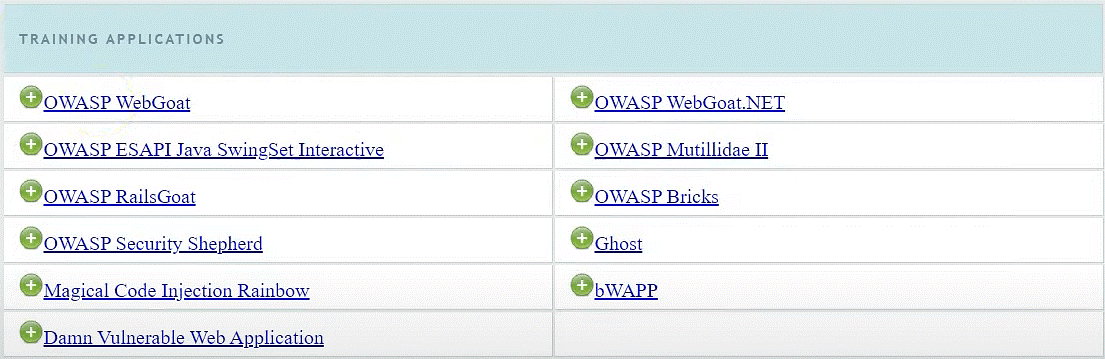
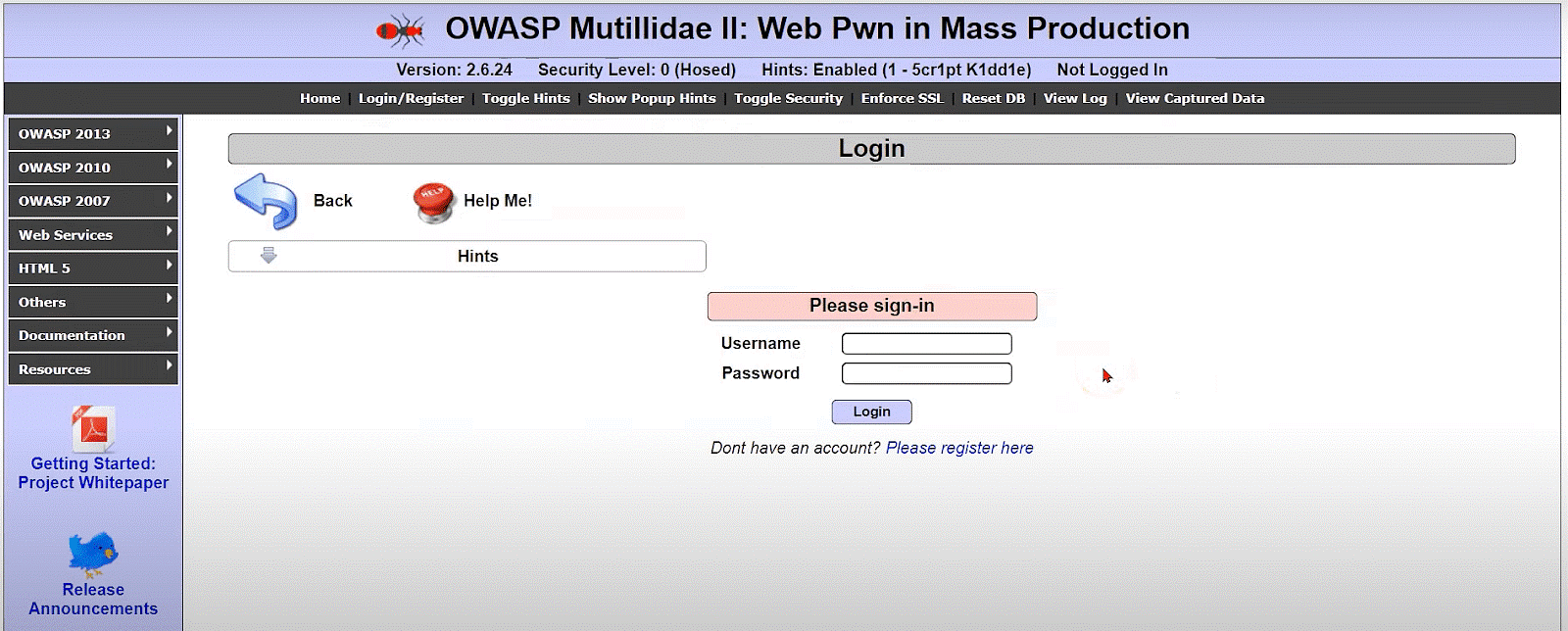
For the demonstration, you’ll be using the OWASP Mutillidae II application.
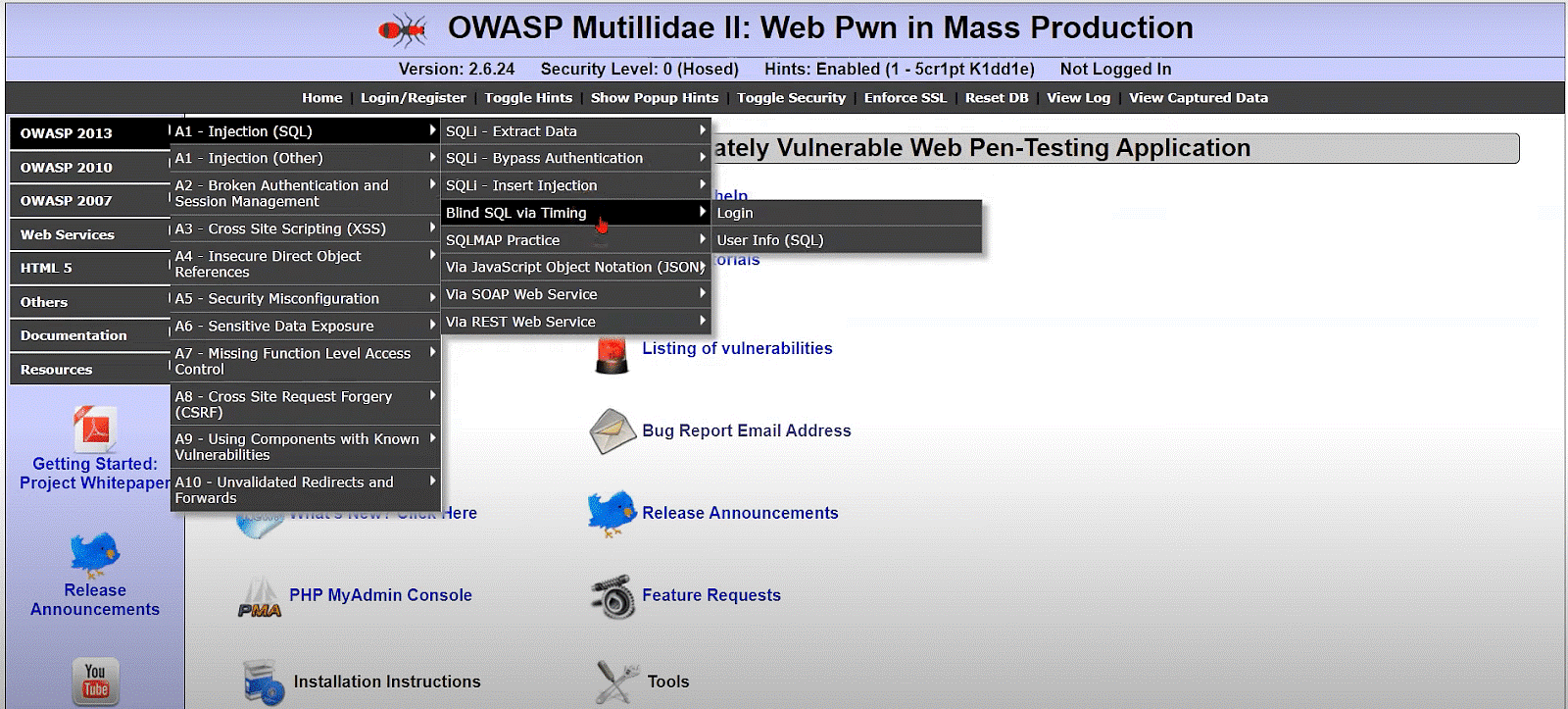
On the left, you can see the OWASP top 10 risks for 2013, 2010, and 2007.
Click on SQLi – Bypass Authentication > Login
You will enter a regular login authentication page that any application may ask for.
Suppose you enter an anonymous username and password, that won’t allow you to log in.
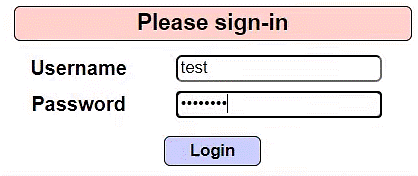
Let’s write an SQL statement in the username and try to login again.
- My Username will be: ‘ or 1=1 —
- Click on Login
- You will log in this will time with a status update saying it has authenticated the user
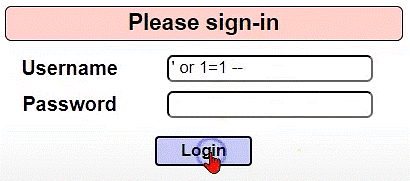
The single quote (‘) is an operator that goes to the database server, selects the default user tables, and compares it to the condition that is given. That condition that you gave was 1=1, which is always true. So, it selected the default user table that was available in the database, and instead of linking it to a password, it compared it to the condition.
If you give a false condition like 1=2, you will get an error message “Account does not exist”.
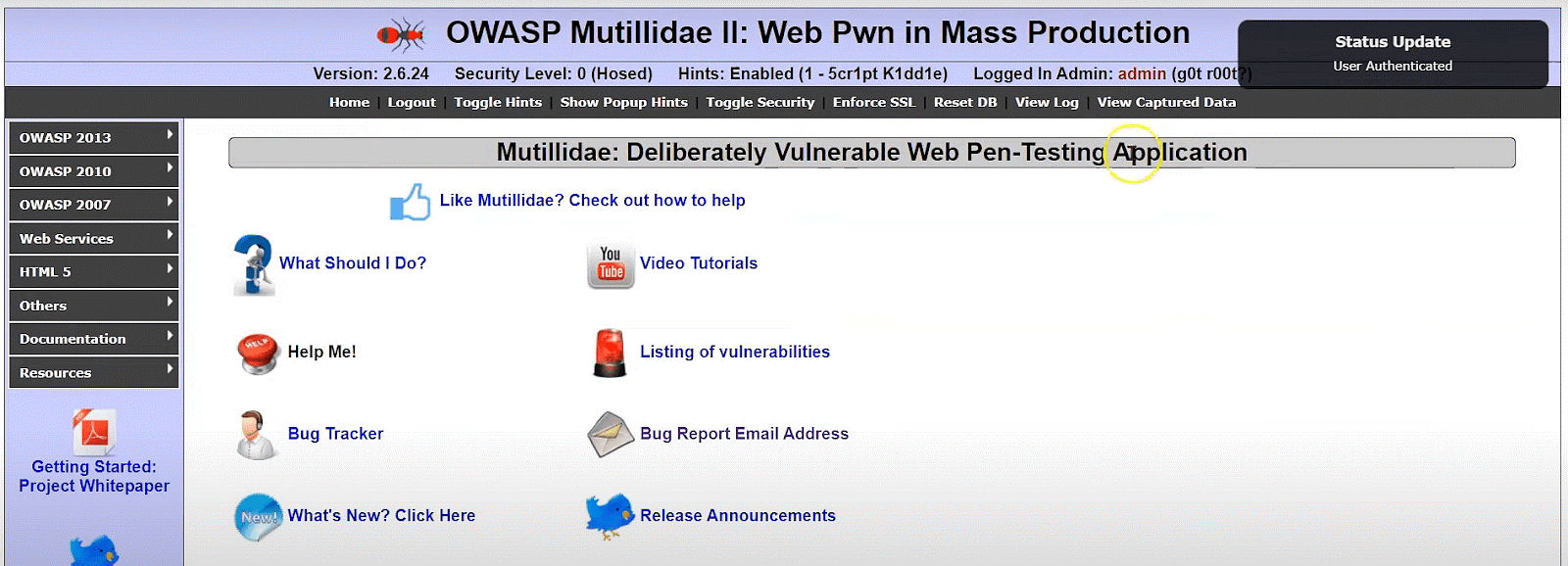
Now, that you have looked at a demonstration on how an SQL query can be used to login to an application.